TalentLMS Single Sign-On Feature And What It Means For You
Doesn't it bother you that in 2016 we still have to carry multiple keys?
House keys, car keys, mailbox keys, office keys, the key for that side door you never use, the list goes on. And we haven't done much better in the digital world, either: We still have to remember a lot of different account credentials to get into all the websites and web services we use.
Wouldn't it be great if you could use the same username and password in numerous places, without the security risk of sharing it among different webpages, and without having to re-enter it?
Thankfully, programmers have come up with several ways to solve this very problem (called "Single Sign-On" in IT speak) - and the best thing is that all the most popular solutions are available in TalentLMS.
TalentLMS Single Sign-On And LDAP
LDAP plays a crucial role in most enterprise Single Sign-On implementations, either as an authentication mechanism itself, or at its most basic role as the industry standard directory service protocol.
In case you are not familiar with the term, a "directory service" is a database of user and organizational data, where enterprises store (and query) employee profiles and authorization information (groups, permissions, etc) -- the IT equivalent of the "Yellow Pages".
Some of the most popular enterprise products based on LDAP are OpenLDAP (a free, open source, LDAP server, popular with Linux-based data centers), and Active Directory, Microsoft's take on LDAP, which we'll talk about in the next section.
On top of its fundamental "directory service" functionality, an LDAP product can also act as an "Identity Provider" for authenticating users. It's this functionality that enables it to be used as an SSO option with TalentLMS.
Connecting TalentLMS to an LDAP server for Sigle-Sign On is quite easy to setup, provided you have a working LDAP identity provider (IdP). You just have to give TalentLMS the URL and Port of your LDAP IdP, and some information about your LDAP schema (e.g. your DN pattern, the attribute you want to be used as the username, etc).
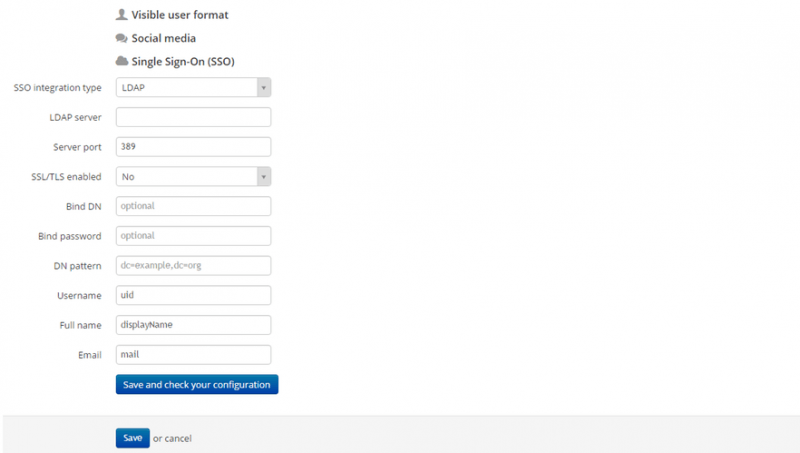
There's a handy setup guide available here.
Active Directory
As we discussed earlier, Active Directory is Microsoft's own take on an LDAP server, with some added bells and whistles, and UI setup convenience.
While Active Directory only runs on Windows, it's (for the most part) compatible with standard LDAP clients, and can be accessed from OS X, Linux and other operating systems just as well. It's also the most popular enterprise directory service option, for businesses of all sizes.
Microsoft's Active Directory Federation Services 2.0 (ADFS 2.0) is an identity provider running on top of Active Directory. TalentLMS can use ADFS for Single Sign-On through its support for (industry standard) SAML (Secure Assertion Markup Language). Under this scheme, ADFS 2.0 handles all user authentication, and any user account changes (e.g. name change, new email, etc.) are synced back to TalentLMS.
Here's how you can integrate Active Directory Federation Services with TalentLMS to allow SSO through SAML 2.0.
Azure Active Directory
Azure is Microsoft's Cloud computing platform (similar to Amazon's AWS and Google's Compute Engine) and it's considered one of the best "infrastructure as a service" Cloud options. It's not tied to Windows application hosting either, with support for Linux (in several flavors) and even special SDKs and environments for Node.js, Java and other popular development technologies.
If you run your LMS or other applications in the Azure Cloud, or just want to take advantage of their federated authentication service, you can integrate TalentLMS with the "Azure Active Directory", Microsoft's identity provider solution for the Azure Cloud, based on (you've guessed it) their Active Directory platform.
Integration with the Azure Active Directory leverages TalentLMS' native support for SAML 2.0 (Secure Assertion Markup Language), the industry standard format for exchanging authentication and authorization information in a platform and provider-agnostic way.
Again, there's a handy guide to configuring TalentLMS to talk to Azure AD here.
SAML 2.0
Thus far we've mentioned SAML in the context of Active Directory related integrations, because those are the most popular SSO options, but SAML is an industry standard of its own, separate from Active Directory and Microsoft, and compatible with many other products and authentication providers.
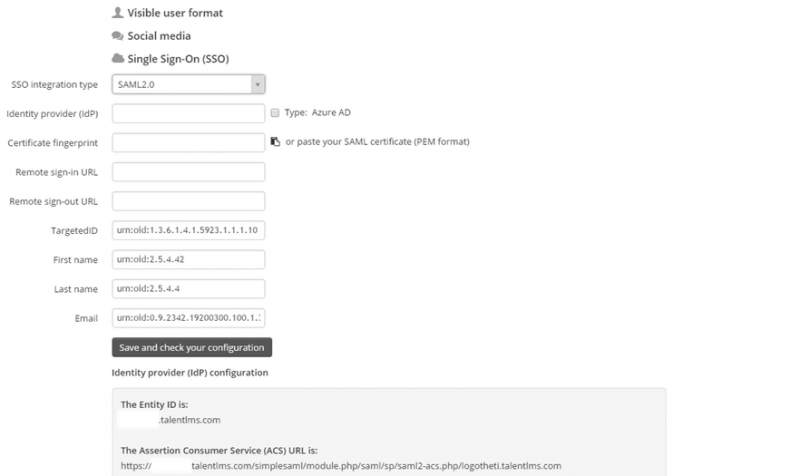
The procedure to configure TalentLMS to delegate authentication services to a third party SAML 2.0 compliant identity provider is documented here.
OneLogin And Okta
These two external identity providers also integrate with TalentLMS through SAML, but since they're quite popular (in general and with TalentLMS users in particular), the TalentLMS team has documented their configuration in more detail here (OneLogin) and here (Okta) respectively.
Conclusion
In this article we had a look at the Single Sign-On options that TalentLMS supports.
Note that TalentLMS Single Sign-On, while nice to have, especially for larger data centers, is actually totally optional. After all, TalentLMS comes with a perfectly good authentication system of it's own.
If you do have a need for SSO though, TalentLMS, with its support for all the most popular industry standard mechanisms should be able to cover it -- and for larger deployments, it even supports connecting to a different Single Sign-On provider per branch.
All options described in the post are equally secure (when configured properly) and battle-proven. Which one is best for your business depends on your existing IT infrastructure and requirements.